-
Written by
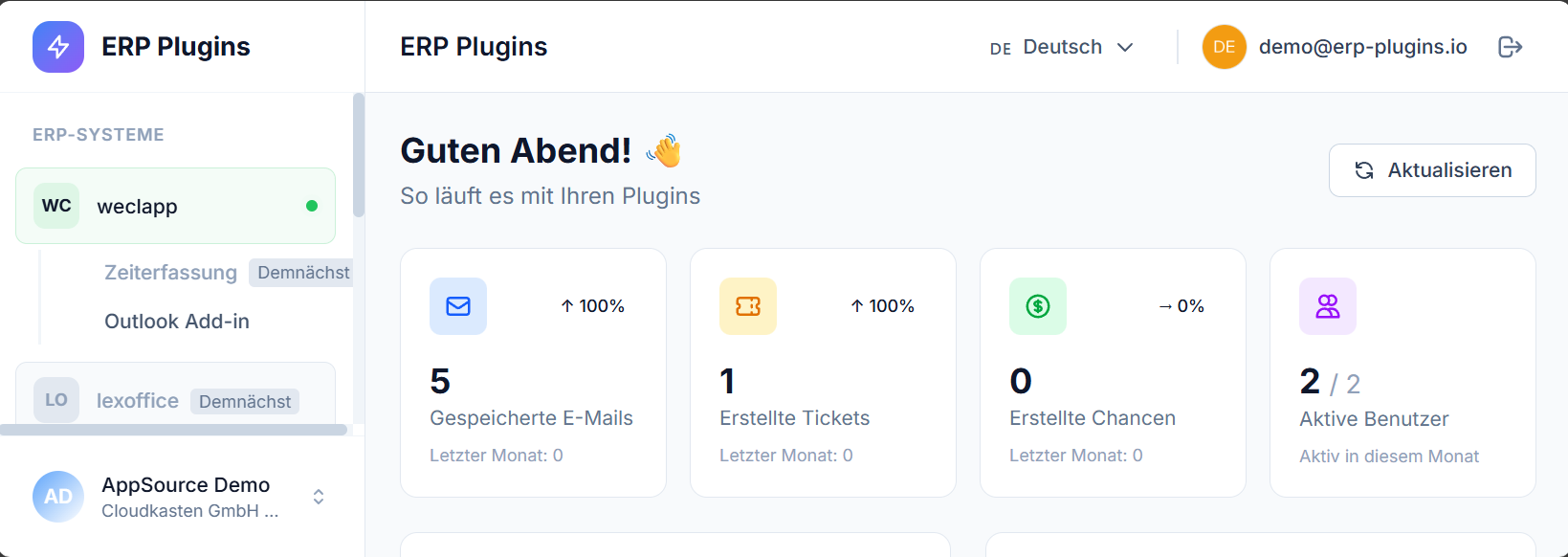
Cloudkasten GmbH
-
Published on
Apr 01, 2026
Share On
NIS2, the EU’s updated directive on cybersecurity and network resilience, came into force across Europe on December 5, 2025. In Germany alone, the scope expanded from roughly 4,500 critical entities to approximately 29,500. If you manage fleet software for transport, logistics, or other essential services, NIS2 is no longer a future concern — it’s an active compliance mandate right now.
And unlike GDPR, which focuses on data privacy, NIS2 is about operational cybersecurity. It covers incident response timelines, supply chain oversight, risk management, and — most notably — personal liability for executives.
This guide walks you through what NIS2 means for fleet management software, and why self-hosted solutions simplify compliance.
What Is NIS2?
NIS2 is the Directive (EU) 2022/2555 on measures for a high common level of cybersecurity across the Union. It replaces the original NIS Directive from 2016 and significantly expands scope, requirements, and penalties.
Key facts:
- Implementation date: December 5, 2025 (EU-wide); Germany implemented via the NIS2UmsuCG law
- BSI registration portal: Opened January 6, 2026
- Registration deadline: March 6, 2026 (already passed for initial registration)
- Scope expansion: From ~4,500 to ~29,500 covered entities in Germany alone
- Penalties: Up to €10 million (€7 million for “important” entities) or 2% global turnover; personal C-suite liability for gross negligence
Unlike GDPR, which regulates how organizations collect and process personal data, NIS2 focuses on protecting critical systems from cyberattacks and ensuring organizational resilience.
Who Must Comply?
NIS2 defines two categories of in-scope organizations:
Essential Entities:
- 250+ employees AND/OR €50M+ annual revenue or balance sheet total
- Operating in critical sectors: Energy, Transport, Water, Healthcare, Digital Infrastructure, Public Administration, Finance, Food Chain, Manufacturing, Waste Management, Chemical, Space
Important Entities:
- 50–249 employees AND/OR €10M–€50M annual revenue or balance sheet total
- Operating in sectors like ICT, Postal/Parcel Services, Space, Digital Providers
Critical for fleet operators: Transport and Logistics are classified as essential sectors. This means most professional fleet operators, logistics companies, bus operators, ride-sharing platforms, and transport authorities fall under NIS2 as essential entities.
Even if your primary business isn’t transport, if you operate fleet software as a critical service, the software and its infrastructure may be classified as essential.
How Fleet Management Software Relates to NIS2
Fleet management systems process data that falls squarely under NIS2 scrutiny:
Operational data:
- Driver profiles and license information
- Booking and dispatch records (who drives what, when, for how long)
- Real-time GPS and vehicle location data
- Historical routing and movement patterns
- Vehicle telematics (fuel, maintenance, error codes)
Risk vectors under NIS2:
- Data sensitivity: Driver locations, personal identifiers, and operational patterns are sensitive operational data.
- System criticality: If your fleet software controls vehicle dispatch or fleet operations, it’s operationally critical.
- Supply chain: SaaS-based fleet software creates a dependency on the vendor’s security posture. NIS2 requires you to audit and monitor this.
- Incident response: If your fleet software is compromised, you must notify the BSI within 72 hours (or 24 hours for early warning, 30 days for final report).
Under NIS2, you’re responsible not just for your organization’s security, but also for overseeing your software vendor’s security if you use a third-party solution.
The 10 Core NIS2 Security Requirements
NIS2 mandates these foundational security controls:
1. Multi-Factor Authentication (MFA) Every user accessing critical systems (including fleet software) must authenticate via at least two factors (password + TOTP, hardware key, biometric, etc.).
2. Encryption
- In transit: HTTPS/TLS 1.2+ for all network communication
- At rest: Disk-level or database-level encryption for sensitive data
3. Role-Based Access Control (RBAC) Users receive only the permissions necessary for their role. No overly permissive accounts.
4. Supply Chain Security If you use SaaS, you must:
- Verify vendor security practices and certifications (ISO 27001, SOC 2, etc.)
- Review Data Processing Agreements for NIS2-specific clauses
- Audit subprocessors (vendors’ vendors)
- Maintain contractual obligations for security updates and breach notification
5. Incident Response & Reporting
- 24 hours: Early warning to national authorities if incident is likely
- 72 hours: Full incident report to BSI
- 30 days: Final report with analysis and remediation steps
6. Risk Management
- Annual risk assessments
- Vulnerability scanning and penetration testing
- Documentation of identified risks and remediation plans
7. Backup & Disaster Recovery
- Regular, tested backups
- Defined Recovery Point Objective (RPO) and Recovery Time Objective (RTO)
- Documented and practiced restore procedures
8. Network Security
- Firewalls and network segmentation
- Intrusion Detection/Prevention Systems (IDS/IPS)
- DDoS mitigation
- Secure network architecture
9. Staff Training & Awareness
- Annual cybersecurity awareness training for all staff
- Incident response drills
- Vendor management training for procurement and IT teams
10. Asset & Configuration Management
- Inventory of all hardware, software, and data assets
- Configuration baselines
- Change management procedures
- Secure disposal procedures for decommissioned assets
Penalties and Personal Liability
NIS2 violations carry severe consequences — far beyond typical regulatory fines:
For Essential Entities:
- Administrative fines up to €10 million or 2% of annual worldwide turnover (whichever is higher)
- Personal criminal liability for executives who fail to implement “appropriate measures” (gross negligence threshold)
For Important Entities:
- Fines up to €7 million or 1.4% of annual worldwide turnover
- Same personal liability
Personal liability is the game-changer. Unlike GDPR, where fines are typically corporate, NIS2 explicitly allows prosecution of individual executives. If your organization suffers a major incident because you ignored NIS2 compliance, the CFO or CTO could face criminal charges.
The German authorities (BSI and prosecutors) take this seriously. Early compliance demonstrates due diligence and protects leadership.
Self-Hosted vs. SaaS: NIS2 Implications
| Aspect | SaaS | Self-Hosted |
|---|---|---|
| Supply chain risk | ⚠️ High — dependent on vendor | ✅ Low — vendor-independent |
| Vendor audits required | ✅ Yes, ongoing | ❌ No |
| Data residency guarantee | ⚠️ Depends on contract terms | ✅ By design — your infrastructure |
| Audit log control | ⚠️ Via vendor | ✅ Direct database access |
| Incident response speed | ⚠️ Depends on vendor SLA | ✅ Immediate — your team |
| MFA configuration | ⚠️ Vendor-dependent features | ✅ Full control |
| Encryption control | ⚠️ Vendor-managed keys | ✅ Your key management |
| Regulatory audit ease | ⚠️ Harder (multi-party) | ✅ Easier (single entity) |
The core difference: With SaaS, you’re auditing a supply chain and relying on contractual obligations. With self-hosted, you own the entire security stack and can demonstrate compliance directly.
For fleet operators in regulated sectors, self-hosted software significantly reduces compliance complexity.
Practical NIS2 Checklist for Fleet Operators
Before deploying or assessing your fleet management software, verify:
- Scope confirmed: Is your organization classified as essential or important?
- Registered with BSI: Does your organization appear on the BSI’s NIS2 entity list?
- Risk assessment completed: Documented risk analysis for your fleet software and infrastructure
- MFA enabled: All user accounts require multi-factor authentication
- Encryption active: HTTPS/TLS in transit, encryption at rest for sensitive data
- RBAC configured: Users have role-specific permissions, not overly broad access
- Audit logging: System logs all data access, modifications, and administrative actions
- Vendor assessment: (SaaS only) Reviewed vendor’s security practices, DPA, and incident response SLA
- Incident response plan: Documented procedures for detecting, reporting, and responding to breaches
- Backup testing: Regular, tested backups with defined RPO/RTO
- Staff training: Annual cybersecurity awareness training completed
- Supply chain review: Documented inventory of all software and infrastructure dependencies
- Compliance documentation: Record of all controls, assessments, and incidents for regulator review
How Self-Hosted Fleet Software Simplifies NIS2 Compliance
Self-hosted solutions like MobilityManager are built with NIS2 compliance in mind:
Data Sovereignty
- Your data stays on your infrastructure — no cloud provider dependencies
- No exposure to foreign jurisdiction claims (like the US Cloud Act)
- Full audit trail under your control
Cryptographic Controls
- End-to-end encryption capabilities
- You manage encryption keys
- Transparent key rotation and management
Immutable Audit Logs
- Every action (login, data access, modification) is logged with timestamp and user ID
- Audit entries cannot be altered or deleted
- Complete forensic trail for incident response and compliance audits
Role-Based Access Control (RBAC)
- Granular permission model
- Users see only data relevant to their role
- Audit trail shows who accessed what and when
Multi-Factor Authentication (MFA)
- Enforced for all accounts
- TOTP-based (Time-based One-Time Password) or hardware keys
- Admin controls for MFA policies
Incident Response Integration
- REST API for integration with SIEM and monitoring tools
- Health check endpoints for continuous monitoring
- Real-time alerting capabilities
- Export functions for rapid incident reporting to BSI
Compliance-Ready Documentation
- Built-in security features reduce the scope of external dependencies
- Simpler audit trails make compliance demonstrations straightforward
- Fewer third-party components to audit and approve
Getting Started: Your NIS2 Implementation Roadmap
-
Assess Your Status
- Confirm you’re in-scope (organization size, sector, location)
- Check if registered with BSI (self-check tool available)
-
Conduct a Risk Assessment
- Inventory all systems used to manage fleet operations
- Identify which systems handle sensitive operational data
- Evaluate current security posture vs. NIS2 requirements
-
Select Compliant Software
- Prioritize self-hosted solutions to reduce supply chain risk
- Verify vendor security practices and certifications
- Ensure software supports MFA, encryption, and audit logging
-
Implement Technical Controls
- Deploy MFA across all administrative and user accounts
- Enable encryption for data in transit and at rest
- Configure RBAC to enforce least-privilege access
- Set up comprehensive audit logging and monitoring
-
Document and Train
- Develop incident response procedures with 24/72/30-hour reporting timelines
- Train staff on NIS2 requirements and their roles
- Create backup and disaster recovery playbooks
-
Monitor and Audit
- Schedule regular risk assessments (at least annually)
- Conduct penetration testing
- Review audit logs for anomalies
- Test incident response procedures quarterly
-
Maintain Compliance
- Keep software and infrastructure patched and updated
- Review supply chain relationships annually
- Document all changes and improvements
- Prepare for potential BSI audits
Conclusion
NIS2 is here, and it’s not going away. For fleet operators — especially those in transport, logistics, and public administration — compliance is a legal and operational necessity.
The good news: self-hosted fleet management software significantly simplifies compliance. By eliminating third-party cloud dependencies, you gain direct control over security, audit trails, and incident response. You can demonstrate compliance to regulators with confidence, and you protect your executives from personal liability.
MobilityManager was built for this reality. With self-hosted deployment, enforced MFA, immutable audit logs, granular RBAC, and full encryption support, it’s purpose-built for organizations navigating NIS2 compliance in the fleet management space.
Ready to ensure your fleet management software meets NIS2 requirements? Schedule a 30-minute demo →